 |
SiteGuard WP Plugin Release 1.7.12 Last update Apr 22, 2026 |
We are currently looking for beta testers for the upcoming version (1.8.0).
Click here for details: WordPress Support Forum
Vulnerability information
| Publication Date | Link |
|---|---|
| March 10, 2026 | Vulnerability in WordPress Plugin "SiteGuard WP Plugin":WPV2026001 |
| May 31, 2024 | Vulnerability in Information Leakage of WordPress Plugin "SiteGuard WP Plugin":WPV2024001 |
Outline
Only installing SiteGuard WP Plugin on WordPress, its security can be improved.
SiteGurad WP Plugin is the plugin specialized for the protection against the attack to the management page and login.
It also have the function to create the exclude rule for WAF (SiteGuard Lite, to use it, WAF should be installed on the Web server.)
Functions list
There are the following functions.
| Admin Page IP Filter | The management directory (/wp-admin/) is protected against the connection source which does not login. |
|---|---|
| Rename Login | The login page name is changed. |
| CAPTCHA | CAPTCHA is added to the login page or comment post. |
| Same Login Error Message | Instead of the detailed error message at the login error, the single message is returned. |
| Login Lock | The connection source which repeats login failure is being locked within a certain period. |
| Login Alert | E-mail notifies that there was login. |
| Fail once | The first login must fail even if the input is correct. |
| Protect XMLRPC | The abuse of XMLRPC is prevented. |
| Block Author Query | Block author query. |
| Updates Notify | If WordPress core, plugins, and themes updates are needed, sends email to notify. |
| WAF Tuning Support | The exclude rule for WAF (SiteGuard Lite) is created. |
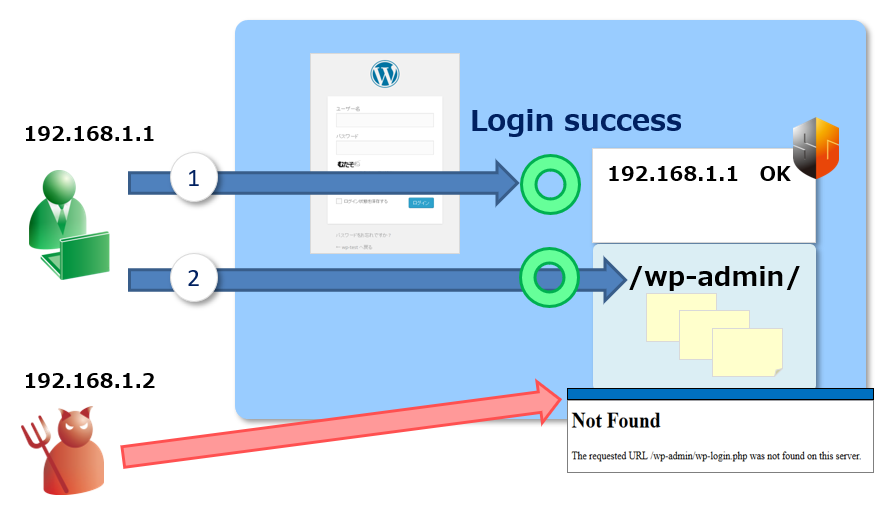
Admin Page IP Filter
It is the function for the protection against the attack to the management page (under /wp-admin/.) To the access from the connection source IP address which does not login to the management page, 404 (Not Found) is returned. At the login, the connection source IP address is recorded and the access to that page is allowed. The connection source IP address which does not login for more than 24 hours is sequentially deleted. The URL (under /wp-admin/) where this function is excluded can be specified.
Rename Login
It is the function to decrease the vulnerability against an illegal login attempt attack such as a brute force attack or a password list attack. The login page name (wp-login.php) is changed. The initial value is “login_<5 random digits>” but it can be changed to a favorite name.
The following access is outside the target of this function.
- Login by the XML-RPC(xmlrpc.php).
- When accessed by specifying the /wp-admin/(Redirect to the login page).
If you want to ban the redirect, please enable the Admin Page IP Filter.
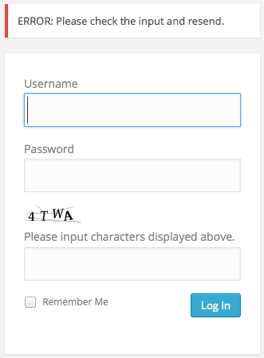
CAPTCHA
It is the function to decrease the vulnerability against an illegal login attempt attack such as a brute force attack or a password list attack, or to receive less comment spam. For the character of CAPTCHA, hiragana and alphanumeric characters can be selected.
Example of hiragana CAPTCHA
![]()
Example of alphanumeric CAPTCHA
![]()
Same Error Messages
It is the function to decrease the vulnerability against the attack to examine if a user name exists. All error messages about the login should be equalized. The following error message is displayed even if anyone of a username, password, or CAPTCHA is wrong.
*Login lock displays a different error message.
Login Lock
It is the function to decrease the vulnerability against an illegal login attempt attack such as a brute force attack or a password list attack. Especially, it is the function to prevent an automated attack. The connection source IP address the number of login failure of which reaches the specified number within the specified period is blocked for the specified time. Each user account is not locked.
At the login lock situation, the following error message is displayed.
![]()
Login Alert
It is the function to make it easier to notice unauthorized login. E-mail will be sent to a login user when logged in. If you receive an e-mail to there is no logged-in idea, please suspect unauthorized login.
Login by the XML-RPC will not be notified.
Fail Once
It is the function to decrease the vulnerability against a password list attack. Even is the login input is correct, the first login must fail. After 5 seconds and later within 60 seconds, another correct login input make login succeed. At the first login failure, the following error message is displayed.
Protect XMLRPC
The pingback function or entier XMLRPC function is disabled and its abuse is prevented.
Block Author Query
Prevents leakage of user names due to “/?author=<number>” access.
Updates Notify
Basic of security is that always you use the latest version. If WordPress core, plugins, and themes updates are needed , sends email to notify administrators. Check for updates will be run every 24 hours.
WAF Tuning Support
It is the function to create the rule to avoid the false detection in WordPress (including 403 error occurrence with normal access,) if WAF ( SiteGuard Lite ) by JP-Secure is installed on a Web server. WAF prevents the attack from the outside against the Web server, but for some WordPress or plugin functions, WAF may detect the attack which is actually not attack and block the function.
By creating the WAF exclude rule, the WAF protection function can be activated while the false detection for the specified function is prevented.
